In an increasingly digital-first world, securing enterprise identities is no longer optional—it's a necessity. Large organizations in the UK are under constant threat from cyberattacks, data breaches, and insider risks. That’s where Identity and Access Management (IAM) and Privileged Access Management (PAM) come into play.
Together, these solutions offer a layered, intelligent approach to safeguarding your data, controlling access, and meeting compliance standards.
What is IAM?
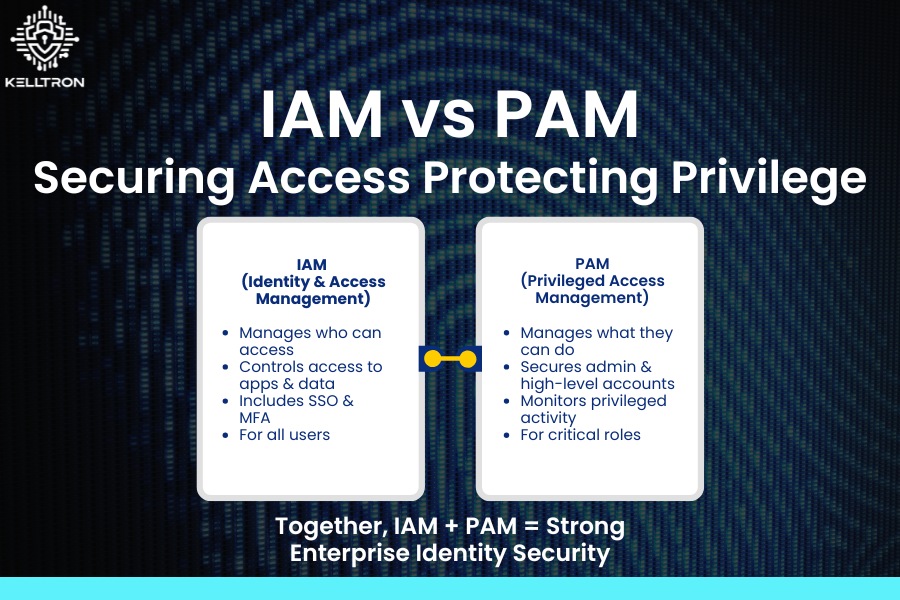
Identity and Access Management (IAM) is the foundation of enterprise identity security. It ensures that only the right people have access to the right systems—at the right time.
IAM services include:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Role-Based Access Control (RBAC)
- Automated User Provisioning
Businesses across the UK are increasingly adopting IAM Implementation Services in London to streamline operations and reduce risks. Whether you're managing on-premise or hybrid environments, Cloud IAM Solutions UK offer secure, scalable identity governance for growing enterprises.
What is PAM?
While IAM controls general user access, Privileged Access Management (PAM) focuses on securing highly sensitive accounts—such as system admins, developers, or database managers.
PAM solutions:
- Vault privileged credentials
- Enforce least-privilege access
- Monitor and record high-risk sessions
- Generate real-time access logs and alerts
With the help of UK-Based PAM Security Experts, organizations can minimize insider threats and comply with data protection regulations more effectively. Privileged Account Security Services UK provide a critical layer of control over elevated access.
Why IAM + PAM = Total Protection
Combining IAM and PAM gives organizations a holistic identity security strategy. While IAM governs identity lifecycle and access policies, PAM protects critical assets and privileged workflows.
Together, they provide:
- Centralized identity and access governance
- Enhanced enterprise data protection
- Automated compliance and audit trails
- Real-time monitoring and control
For organizations aiming to strengthen their Enterprise Data Governance UK capabilities, this integrated approach is essential.
Implementation Strategy
Here’s a roadmap for deploying IAM and PAM in your enterprise:
- Assess – Conduct an audit of all digital identities, permissions, and privileged accounts.
- Implement IAM – Deploy secure authentication and access control with support from Identity and Access Management Services UK.
- Add PAM – Safeguard high-risk access points with Privileged Access Management Solutions UK.
- Govern & Monitor – Partner with a Data Governance Consulting Firm UK for policy oversight and continuous monitoring.
- Optimize – Use behavioral analytics to detect threats and adapt policies in real time.
Why Choose Kelltron?
At Kelltron, we specialize in Secure Data Management Consulting UK, delivering tailor-made solutions for your identity and access needs. From Product Information Management Systems UK to full IAM/PAM integration, we help you protect what matters most.
Ready to secure your organization? Let’s build a safer, smarter future together.
Contact us today to learn more about our Identity and Access Management solutions in the UK.